As technology continues to advance, so do the threats and risks to our cybersecurity. One of the most common defenses against these threats is the use of firewalls and intrusion prevention systems (IPS). However, these systems are not foolproof and can encounter problems that may leave your organization vulnerable to attacks.
One of the most common issues with firewalls and IPS is misconfiguration. This can occur when the system is set up incorrectly or when changes are made without proper testing or documentation. Misconfiguration can result in false positives or false negatives, where legitimate traffic is blocked or malicious traffic is allowed through. This can leave your organization exposed to potential cyberattacks.
Another problem with firewalls and IPS is that they can be bypassed by skilled hackers. This is often done through advanced tactics such as exploiting vulnerabilities in the system, using evasion techniques to avoid detection, or even social engineering attacks that trick users into allowing access. As technology continues to advance, hackers are finding new and creative ways to circumvent these security measures.
In addition to these technical challenges, firewalls and IPS can also be limited by human error. This can include not properly updating the system with the latest security patches, not properly monitoring the system for anomalies, or not responding to alerts in a timely manner. All of these factors can leave your organization vulnerable to attacks.
To mitigate these problems, it's important to regularly review and update your firewall and IPS systems, train your employees on proper cybersecurity practices, and have a solid incident response plan in place. Additionally, consider implementing a multi-layered defense strategy that includes other security measures such as endpoint security, DNS layer security, and identity service engine (ISE).
Let’s review from Cisco Secure Firewall Management Center these intrusion policies. We see that SFMC has scored rules based on overhead.
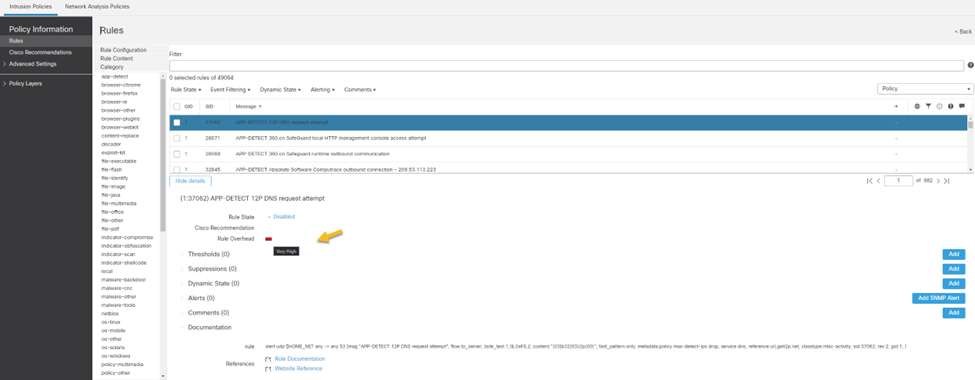
Overhead has four levels “Low”, “Medium”, “High”, and “Very High”. Each of these levels corresponds with an intrusion base policy.
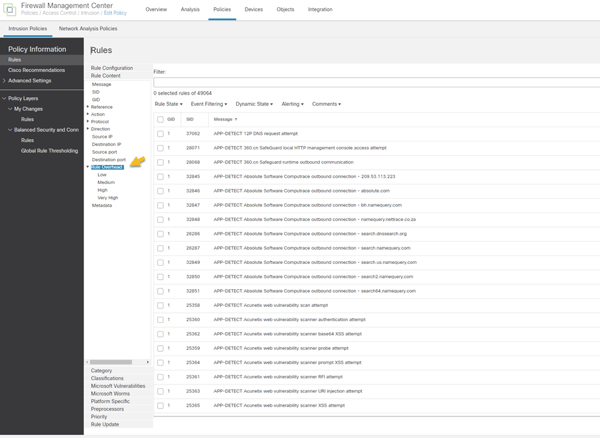
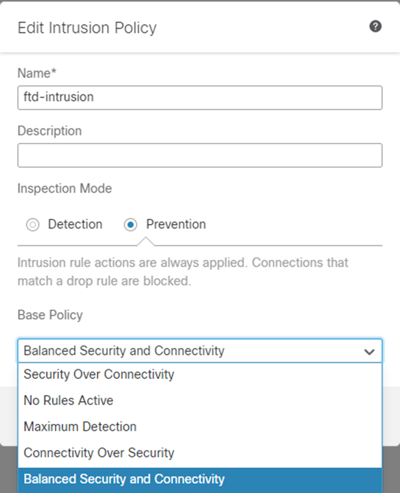
Low = “Connectivity over Security”
Medium = “Balanced Security and Connectivity”
High = “Security over Connectivity”
Very High = “Maximum Detection”
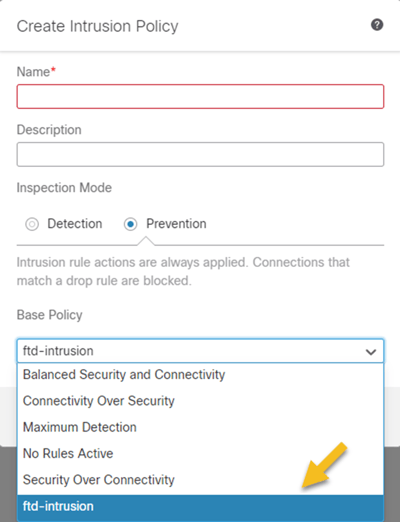
Each of these base policies just enables more rules increasing detection, but also “overhead” on the firewall. So user beware on what base policy you choose. We can choose to create our own base policy templated after a custom intrusion policy as shown below.
In conclusion, firewalls and intrusion prevention systems are crucial components of a robust cybersecurity strategy. However, they are not infallible and can encounter problems that leave your organization exposed to attacks. By staying vigilant, regularly reviewing and updating your systems, and implementing a multi-layered defense strategy, you can better protect your organization from potential cyber threats.
As always if you have any questions on getting Cisco Secure Firewall Management Center set up for you and your business and would like to schedule a free consultation with us, please reach out to us at sales@lookingpoint.com and we’ll be happy to help!
Pablo Mirsoian, Network Engineer




