It’s our favorite time of year again – October. This love for October is more than the fall weather, leaves changing, upcoming holidays and pumpkin spice everything. October is National Cyber Security Awareness Month and here at LookingPoint we love cybersecurity.
We’re all aware of the potential dangers of hackers, malware, phishing attacks, ransomware and the list goes on. As we continue to integrate our businesses more digitally we can be certain of two things – cyber-threats will continue to exist and continue to evolve and the need to do digital business will remain foundational to an organization’s success. Cybersecurity is no longer a new or segmented aspect of IT, it is something that must be integrated into every aspect of business operations.
According to the Ponemon Institute, 1/3 of all attacks are projected to utilize fileless techniques in 2018. Firewalls and anti-virus tools are no longer enough to keep your business secure from emerging cyber threats. To keep your business secure you need to implement processes and tools that will help identify, protect, detect, respond and recover from a cyber-attack.
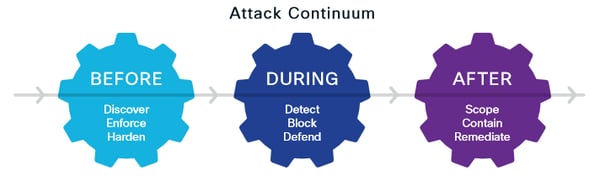
- Identify – the first step in protecting your business is identifying the assets and systems that are critical to the business as well as the potential threats that could compromise those assets. If you have assets that would make it hard to run the business should they be compromised, you also have a valuable target for cybercriminals. Clearly identify and document what these assets are and have the right backups in place to prevent disruptions in your business should they be compromised.
- Protect - Identifying your valuable business assets and potential threats is only the beginning. Once you have identified these assets you now must implement the right technology and processes to protect them. When evaluating your existing infrastructure and potential improvements or additions to your cybersecurity portfolio you want to consider the following:
- Network segmentation - dynamically controlling network access helps reduce exposure across the network if it is compromised.
- Next-generation firewall - block more threats and quickly mitigate the ones that do breach your defenses with a threat-focused firewall.
- Virtual Private Network – extend your private network across public networks to allow employees to securely send and receive data.
- DNS protection – cloud-delivered security at the DNS and IP layers can protect any device, anywhere.
- Anti-malware protection – protect your entire business from endpoints to emails and the network level.
- Two-factor authentication – utilize an additional layer of security to check credentials of those accessing your network.
Technology is only one aspect to protecting your business from cyber-threats. Keeping your infrastructure current with the latest software, web browser and operating system patches and updates will help defend against online threats. Continued employee education about security policies and vigilance when opening emails or attachments will also help to protect your business from cyber-threats.
- Detect – we do all we can to protect our business from cyber-threats, but no business is impenetrable. Your ability to quickly detect and mitigate a cybersecurity breach will minimize the impact it has on your business. Advanced malware protection not only protects your business from breaches, it also provides the visibility, context, and control to rapidly detect, contain, and remediate threats if they evade front-line defenses.
- Respond – have a documented plan in place before a breach occurs to quickly contain the attack and minimize business impact. It’s important that your response plan addresses how to contain an attack, where your backup data is stored and how to ensure it remains protected, appropriate escalation of a breach, and any industry or company policies and guidelines to follow should a breach occur.
- Remediate – after an attack the goal is to restore normal systems and operations back to the business as quickly as possible. The right data backup and recovery solution will alleviate a lot of the heavy lifting from your IT team. The key in quick remediation is consistent backup and good documentation. During remediation you should take time to document the breach – where your network was vulnerable, what impact that breach had, how quickly it was contained and remediated and what steps need to be taken to prevent future breaches.

LookingPoint is committed to providing our customers with the most secure technology solutions and services on the market. We frequently evaluate new solutions and stay up to date with the latest breaches and how to prevent them. One of the best ways to see how secure your business is and how prepared you are to respond to a cyber-attack is through a security assessment.
Written By: Eden Reid, LookingPoint Marketing Manager




