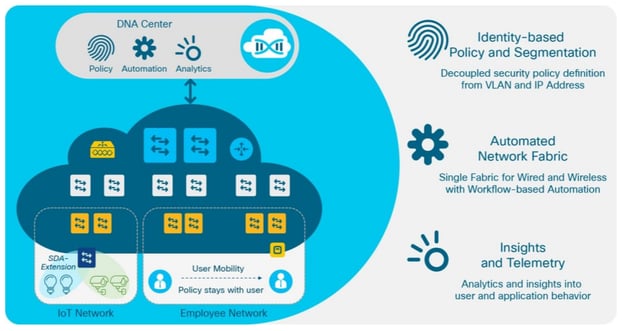
Earlier this year Cisco released their new Digital Network Architecture (DNA), which they are calling “intent-based networking”. Cisco DNA is an open, programmable architecture that turns business intent into business results, and is the foundation for The Network. Intuitive. Cisco also released their Software-Defined Access (SD-Access) solution, which is the “industry’s first intent-based networking solution for the Enterprise built on the principles of Cisco’s DNA”. SD-Access provides
- Automated end-to-end segmentation with identity-based policy, regardless of location
- Automated user access policies
- Consistent user experience anywhere without compromised security through a single network fabric across LAN and WLAN

In more pointed terms SD-Access is Cisco’s introduction of software defined networking for the access layer of campus and branch office networks.
Back in July LookingPoint Consulting Services SME, Dominic Zeni, wrote about SD-Access, the problems it solves, and how it compares to Cisco’s Campus Fabric solution. I wanted to dive less into the technical aspects of SD-Access, and more into the “who and how” of the solution. Who should be looking at SD-Access or something like it and how exactly do you deploy it?
“Every company should be looking at something like SD-Access, and eventually will be” – Dominic Zeni. Today many companies are facing the challenges of manual network turns ups. I’m sure many of you are familiar with this scenario: your IT administrator is responsible for 100 branch offices and is getting bombarded with requests from different business units to turn up new network services, and just can’t keep up. SD-Access helps to solve this challenge through automation. With the increase in security threats, especially throughout 2017, more and more companies are also focused on security. However, when it comes to IT teams working to get the network up and running, security has become an afterthought. SD-Access has security policies built in, so security protocols and policies are applied as the same time you are provisioning the network. Everyone should be looking at something like SD-Access, especially companies who want to improve security policy and eliminate “human error” when provisioning or making changes to the network.
When considering deploying SD-Access it is likely most customers have most of what they need. Any customer who has been keeping their network environment up to date likely has the switches, access points and wireless LAN controllers needed to support the SD-Access solution. If your environment has not been refreshed recently it is possible you may need to do a hardware refresh. You will also need to get the back-end applications needed to support the solution, such as DNA Center. Other than an up-to-date environment, and back-end applications all you need to deploy SD-Access is to bring your own IP network. SD-Access is built on top of your current network adding intelligence and automation from the controller aspect.

One tip that is not “required” for SD-Access, but is a focal point of ensuring security is to consider deploying Cisco ISE. SD-Access is not needed to deploy Cisco ISE, and it is a great starting point for securing your environment. Regardless of the network switching or wireless LAN equipment deployed in your network you can (and should) implement a network access control solution like Cisco ISE, and start requiring devices to authenticate to access your network.
In simple terms SD-Access provides:
- Centralized configuration management
- Automation and policy control
- Ensured security
- Real time telemetry and metrics to make decisions based on
Watch our Fireside Chat to learn more about SD-Access.
Written By: Eden Penman, LookingPoint Marketing Manager



