Welcome back! In this blog we’re going to continue where we left off in the last entry where we looked at using Microsoft Intune to provision the native wired 802.1x supplicant on Windows 10. This time, we shift our focus to the wireless 802.1x supplicant. If you missed that one, be sure to check it out! OK! Let’s go!
Reiterating the Assumptions!
It is not my goal (or desire!) to cover all the pre-requisites in this write up, so let’s establish a few assumptions around the existing environment.
- We will be pretending that Microsoft Active Directory DOES NOT EXIST! (So that we can’t leverage any functionality provided by it) Welcome to the brave new world.
- A SCEP (Simple Certificate Enrollment Protocol) server has already been instantiated and we have in our possession the SCEP enrollment URL to provide to our Intune configuration profile. In our case, we are leveraging a private, SaaS delivered PKI by the name of SecureW2.
- The Windows10 endpoints we are targeting with these configuration profiles have already been enrolled as corporate owned devices into MS Intune. They are Azure AD joined as well, although this bit is not relevant for this procedure (you could follow the same procedure for a Windows 10 personal device if you allow those to enroll to your MS Intune).
- We have, in fact, already provisioned the SCEP configuration profile for our Windows 10 devices (both device and user certificates).
Windows 10 – Wireless Supplicant Provisioning
Since we already have the SCEP configuration and our Trusted Certificates in place, there is only one bit left to do.
#1 – Configure the Windows 10 Wi-Fi Configuration Profile Template in MS Intune! Go! Go! Go!
Wireless Configuration Profile
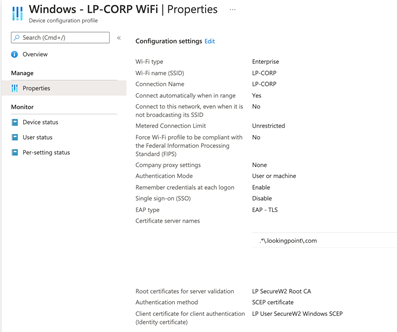
Unlike pushing a wired 802.1x configuration from Intune, which we had to leverage a “Custom” profile type, Intune has a pre-built template for this! While this pre-built template is not up to date (yet) with the newest and coolest 802.1x EAP method on the block (EAP-TEAP), it will be able to support 99% of the deployments currently in the wild. All of this is done through Microsoft Intune administration at https://endpoint.microsoft.com/.
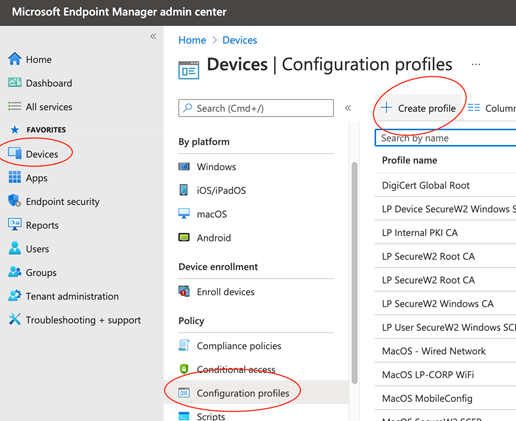
Begin by navigating to Devices > Configuration Profiles > Create Profile.
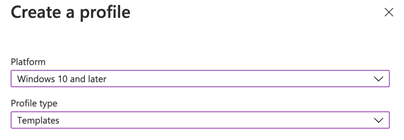
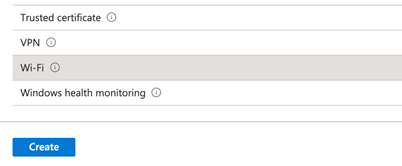
Select Windows 10 for Platform, Templates for Profile Type, and Wi-Fi for Template Name. Create!
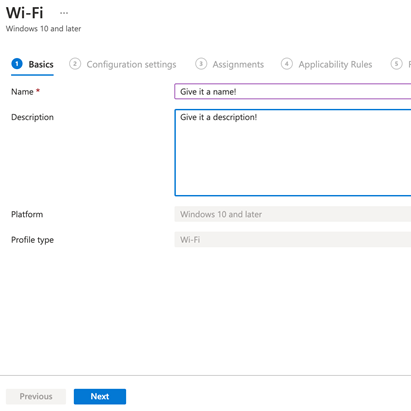
Give it a Name! Give it a Description! Click Next!
The example below is setup to use EAP-TLS! Note that even though the “User” SCEP profile was selected in the configuration, through testing we were able to validate both User OR Computer were able to successfully authenticate to this network! Ensure you scope this to all devices! Create!
What’s Next?
This was a quick and dirty (and admittedly rough around the edges) look at central provisioning of the wireless native 802.1x supplicant in Windows10 via Microsoft Intune. In the next entry in this series, let’s look at integrating MS Intune as an MDM into ISE so that we may perform some Authorization checks against these Authentications (remember, no AD)! Thanks for reading!
As always if you have any questions on getting Cisco's ISE set up for you and your business and would like to schedule a free consultation with us, please reach out to us at sales@lookingpoint.com and we’ll be happy to help!
Want the answers to the most asked questions about ISE? Check out our video below!
Dominic Zeni, LookingPoint Consulting Services SME - CCIE #26686




