How to create a Certificate Signing Request with OpenSSL for your Cisco Firepower Threat Defense Firewall managed by FirePower Management Center.
Fewer and fewer ASA firewalls in production as time goes on. They usually get replaced with Cisco’s FirePower Threat Defense. FTD for short. These FTDs in turn are managed usually by FirePower Management Center. ASDM managing your firewalls are gone when moving to the FTD platform. ASDM allowed us to create CSR to use for our Remote Access VPNs, but it also seemed to have limitations as well. I always had problems creating CSRs with Subject Alternative Names (SAN) records. For the FTD OpenSSL is the best method. My hope for this guide is to cut through all the confusion and get you up and running with a complete certificate chain in your FMC store.
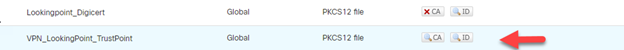
One common misconfiguration I see a lot in the FMC are the PKCS12 file containing private key, identity certificate, intermediate certificate and root certificate. For a proper PKCS12 file all you will need is private key, identity certificate, intermediate certificate. If you follow my steps, you’ll get something like the bottom trustpoint a complete certificate chain with no errors.
For the OpenSSL program that I’m using is Cygwin since I’m on a Windows 10 device. If you’re on Mac OSX or Linux you can open up a Terminal window. Program like Cygwin allows you to use open source tools like OpenSSL.
***Disclaimer***
Use and Install Cygwin at your own risk.
Once you have Cygwin installed and have your Terminal open type the following commands to create a Certificate Signing Request.
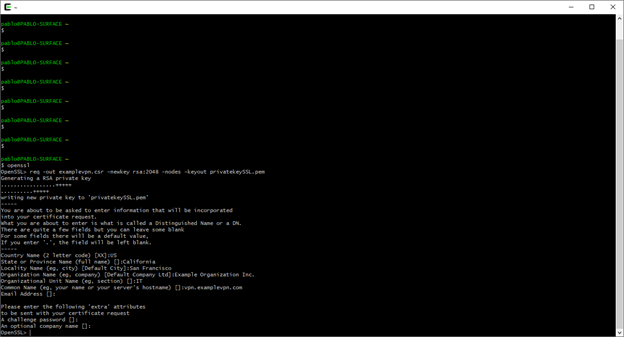
Here is a breakdown of the OpenSSL commands used above.
Openssl req -out examplevpn.csr -newkey rsa:2048 -nodes -keyout privatekeySSL.pem
req – certificate request and certificate generating utility in OpenSSL.
-out examplevpn.csr – name certificate examplevpn.csr as Certificate Signing Request
-newkey rsa:2048 – generate a new private key and certificate request using 2048 key strength
-nodes – no not encrypt private key pem file
-keyout privatekeySSL.pem – use the indicated privatekeySSL.pem as the private key file
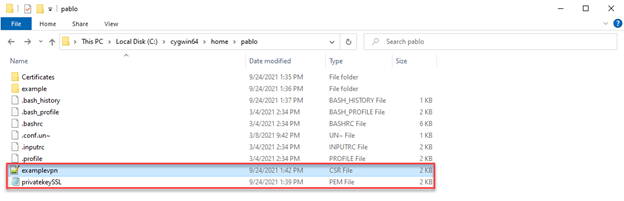
This creates two files a examplevpn.csr and a privatekeySSL in your Cywgin home folder.
What if we wanted to create a CSR with Subject Alternative Names?
To facilitate this process, I use a simple configuration file for openssl to reference.
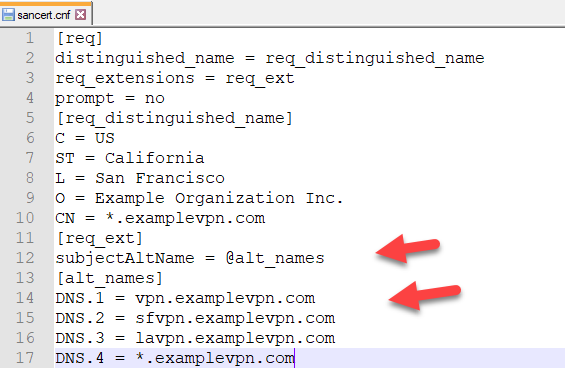
Add this sancert.cnf file to Cygwin home folder.
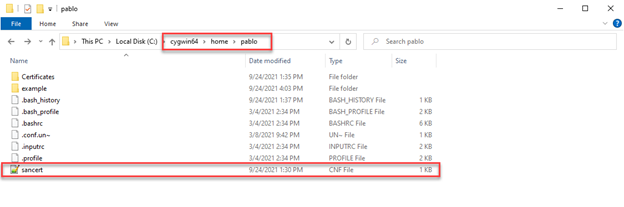
What this file also does is answer all those attribute questions that we saw in our first CSR file creation.
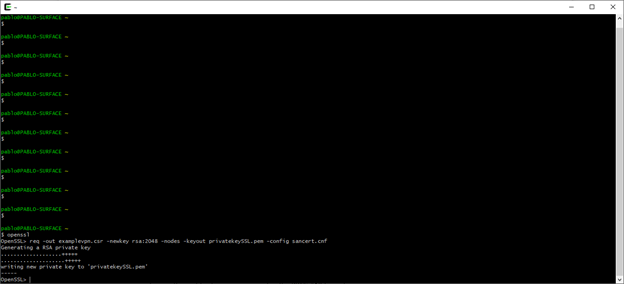
-config sancert.cnf – calls upon this configuration file for all the attributes.
I’ll go to a CSR decoder website to validate the CSR files. This will show if all the attributes are correct.
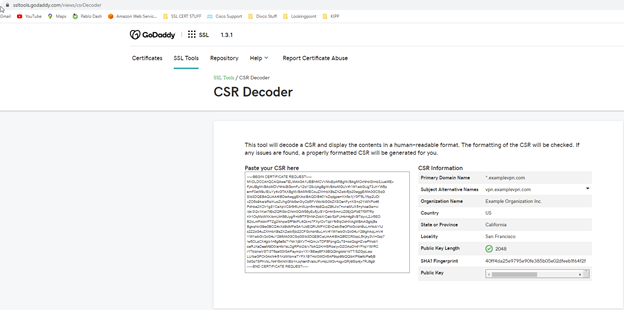
At this point you would submit the CSR to your domain registry. Cisco provides a good example using GoDaddy.
Once you get your Zip file this will usually contain your Identity Certificate, Intermediate Certificate, and Root Certificate.
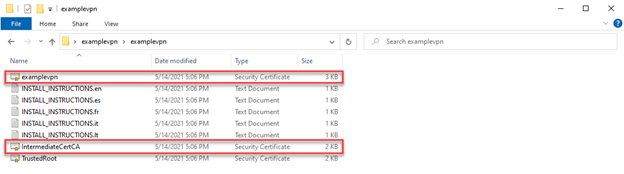
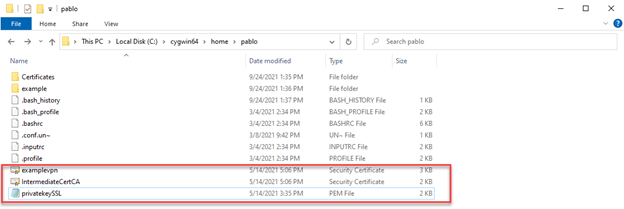
What is important are the files called out in red. Identity Certificate and Intermediate. We want to copy those files to our home folder and our private key pem file.
From here we can bundle our Private Key, Identity Certificate and Intermediate Certificate into a PKCS12 file for FTD upload.
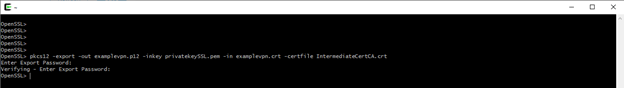
-pkcs12 – calls for the PKCS12 utility in OpenSSL.
-export – argument that calls for a PKCS12 to be created.
-out examplevpn.p12 – PKCS12 filename.
-inkey privatekeySSL.pem – use this private key file.
-in examplevpn.crt – use this certificate.
-certfile IntermediateCA.crt – this is an option to read from addition certificate files.
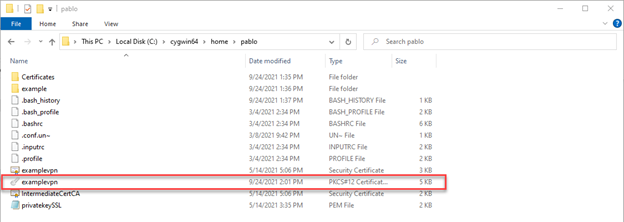
When all is said and done, we should see a new file in our home folder. Our PKCS12 file that our FMC can now use to upload too.
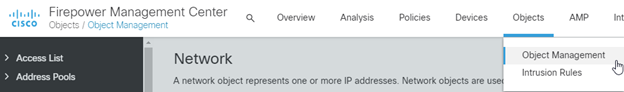
Log into our FMC and head to our Object Management.
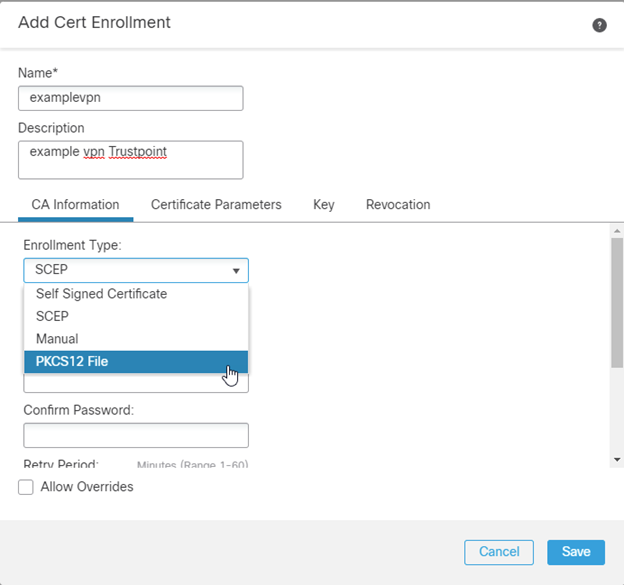
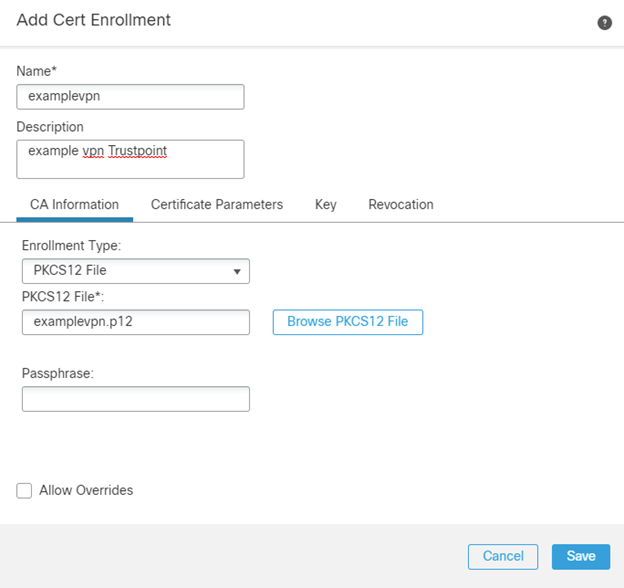
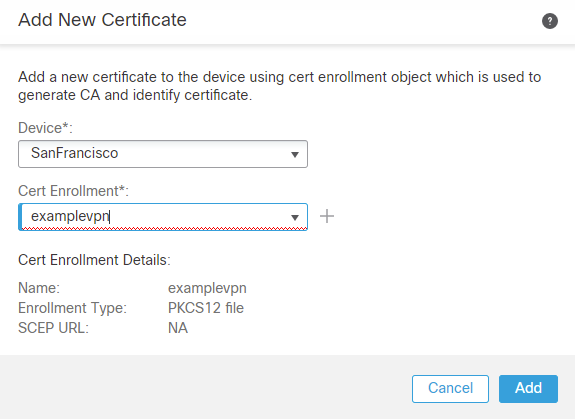
Head to PKI section, Cert Enrollment and Add Cert Enrollment

Name your Trustpoint and select PKCS12 File as the enrollment type.
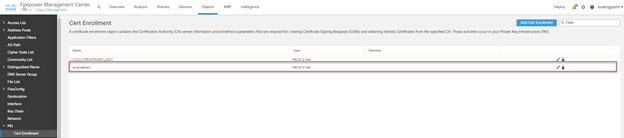
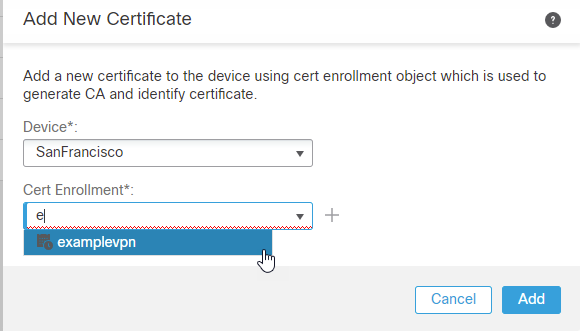
Now we will want to navigate to the Certificate store on the FMC.
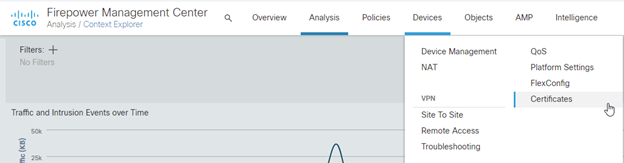
Here we will add the PKCS12 file to the appropriate FTD that’s hosting the Remote Access VPN.
After import we should see something like this….A complete chain and no errors.

Last step is to tell the FTD to use the new Trustpoint for Remote Access VPN.
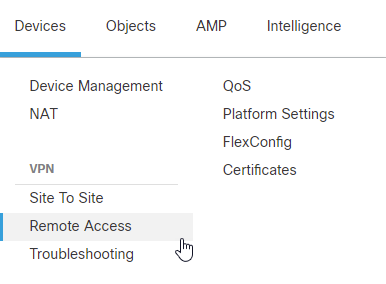
We head to Devices and Remote Access.
Open or edit our Connection Profile….

Associate new trustpoint SSL certificate.
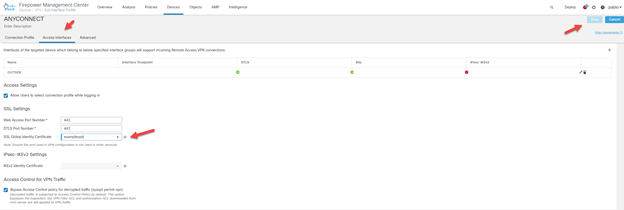
Save and deploy.
After the FMC has deployed to the FTD we can test our VPN connection by using either Anyconnect VPN client or web browsing to the url of the vpn address. There you can inspect the SSL cert via your browser.
As always if you have any questions on getting FMC set up for you and your business and would like to schedule a free consultation with us, please reach out to us at sales@lookingpoint.com and we’ll be happy to help!
Pablo Mirsoian, Network Engineer




