
Project Manager: “We need to give them access to our network.”
IT Security: “No.”
Project Manager: “We really need to give them access to our network.”
IT Security: “Still no.”
Project Manager: “C’mon, pleeease??”
IT Security: “Ok fine. But we’ll need to assess their computer for vulnerabilities.”
Third times a charm! Do you need to allow remote access into your network? Do you need to ensure the endpoints connecting to your network meet your security requirements? If you answered yes, then this blog series is for you!
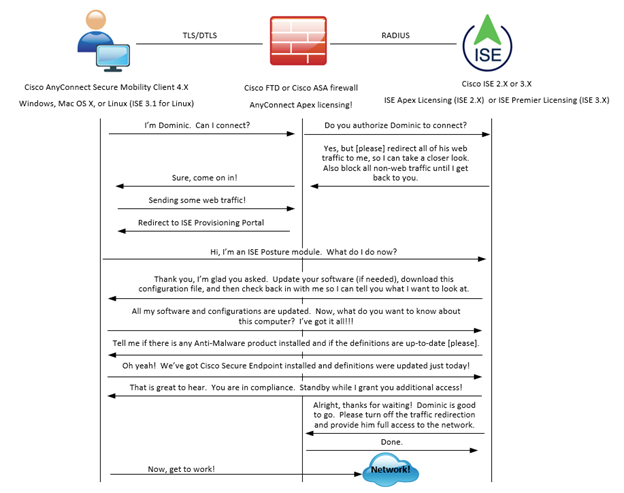
In this series we will be covering the AnyConnect ISE Posture for VPN clients connecting through a Cisco FTD/ASA firewall. This initial entry is going to give a high-level tour of the components and mechanics involved to ascertain the security posture of AnyConnect VPN clients using Cisco ISE. Onward!
The Components
Let’s begin by identifying all the players in the solution! You will need the components outlined below.

The AnyConnect client serves as the Posture Agent in this solution by way of installing a special module called, you guessed it, the ISE Posture module. The ways and means of provisioning the ISE posture module are plenty, and we won’t be getting into that in this write up. For this post, we can safely assume that the AnyConnect client + ISE Posture module have been previously installed. As the landscape of security applications/vendors is constantly evolving (or re-branding it seems like mostly these days…but I digress), we need a way to evolve with it! We can’t get stale! As opposed to having to update the AnyConnect client main package when these evolutions happen, the ISE posture module loads a “compliance module”. This compliance module is updated by Cisco as needed and these updates are pushed dynamically, albeit controllably, to the AnyConnect ISE Posture module by way of the ISE Client Provisioning Portal. I like to think of the compliance module as being analogous to anti-malware definition files, though they are updated with less frequency. So, the “compliance module” keeps the AnyConnect client up to date with the latest endpoint security/OS updates, but how about ISE itself? Glad you asked. ISE maintains a connection to Cisco’s Posture Feed Service and regularly checks in to update its posture catalog with the latest ongoings in the industry. Good! Moving on.
When the AnyConnect client makes a request to join the VPN, the ASA/FTD sends a message to ISE to authenticate/authorize the AnyConnect client access to the network. ISE will send back instructions to the ASA inside of a RADIUS authorization that will set into motion the posturing of the endpoint. This leads us nicely into…
..The Mechanics!
Here we will focus on the interesting bits as it relates to ISE ascertaining the posture of the endpoint running the AnyConnect client. As this is the high-level overview, we’re skipping a lot of the details. We’ll get into that next time. For now, enjoy this ladder diagram anthropomorphizing the AnyConnect client, the ASA/FTD, and ISE.
What’s Next?
Now that we’ve surveyed the land, in the next post we’ll break out the hand shovel, turn some dirt over, and dig in a little deeper. We will go into the details of how the AnyConnect client gets provisioned! Thanks for reading.
As always if you have any questions on getting Cisco's ISE set up for you and your business and would like to schedule a free consultation with us, please reach out to us at sales@lookingpoint.com and we’ll be happy to help!
Want the answers to the most asked questions about ISE? Check out our video below!
Dominic Zeni, LookingPoint Consulting Services SME - CCIE #26686




